Enterprise permissions
This feature is limited to the dbt Cloud Enterprise plan. If you're interested in learning more about an Enterprise plan, contact us at sales@getdbt.com.
The dbt Cloud Enterprise plan supports a number of pre-built permission sets to help manage access controls within a dbt Cloud account. See the docs on access control for more information on Role-Based access control (RBAC).
Roles and permissions
The following roles and permission sets are available for assignment in dbt Cloud Enterprise accounts. They can be granted to dbt Cloud groups which are then in turn granted to users. A dbt Cloud group can be associated with more than one role and permission set. Roles with more access take precedence.
The user's license type always overrides their assigned permission set. This means that even if a user belongs to a dbt Cloud group with 'Account Admin' permissions, having a 'Read-Only' license would still prevent them from performing administrative actions on the account.
Key:
- (W)rite — Create new or modify existing. Includes
send,create,delete,allocate,modify,develop, andread. - (R)ead — Can view but can not create or change any fields.
Permissions:
- Account-level permissions — Permissions related to the management of the dbt Cloud account. For example, billing and account settings.
- Project-level permissions — Permissions related to the projects in dbt Cloud. For example, repos and access to the dbt Cloud IDE or dbt Cloud CLI.
Account roles
Account roles enable you to manage the dbt Cloud account and manage the account settings (for example, generating service tokens, inviting users, and configuring SSO). They also provide project-level permissions. The Account Admin role is the highest level of access you can assign.
Account permissions for account roles
| Account-level permission | Account Admin | Billing admin | Manage marketplace apps | Project creator | Security admin | Viewer |
|---|---|---|---|---|---|---|
| Account settings | W | R | R | R | ||
| Audit logs | R | R | R | |||
| Auth provider | W | W | R | |||
| Billing | W | W | R | |||
| Groups | W | R | W | R | ||
| Invitations | W | W | W | R | ||
| IP restrictions | W | W | R | |||
| Licenses | W | W | W | R | ||
| Marketplace app | W | |||||
| Members | W | W | W | R | ||
| Project (create) | W | W | ||||
| Public models | R | R | R | R | R | |
| Service tokens | W | R | R | |||
| Webhooks | W |
Project permissions for account roles
| Project-level permission | Account Admin | Billing admin | Project creator | Security admin | Viewer |
|---|---|---|---|---|---|
| Data platform connections | W | W | R | ||
| Environment credentials (deployment) | W | W | R | ||
| Custom env. variables | W | W | R | ||
| Data platform configurations | W | W | R | ||
| Develop (IDE or dbt Cloud CLI) | W | W | |||
| Environments | W | W | R | ||
| Jobs | W | W | R | ||
| Metadata GraphQL API access | R | R | R | ||
| Permissions | W | W | W | R | |
| Profile | W | W | R | ||
| Projects | W | W | R | R | |
| Repositories | W | W | R | ||
| Runs | W | W | R | ||
| Semantic Layer config | W | W | R |
Project role permissions
The project roles enable you to work within the projects in various capacities. They primarily provide access to project-level permissions such as repos and the IDE or dbt Cloud CLI, but may also provide some account-level permissions.
Account permissions for project roles
| Account-level permission | Admin | Analyst | Database admin | Developer | Git Admin | Job admin | Job runner | Job viewer | Metadata (Discovery API only) | Semantic Layer | Stakeholder | Team admin | Webhook |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Account settings | R | R | R | R | |||||||||
| Auth provider | |||||||||||||
| Billing | |||||||||||||
| Groups | R | R | R | R | R | R | |||||||
| Invitations | W | R | R | R | R | R | R | R | R | ||||
| Licenses | W | R | R | R | R | R | R | R | |||||
| Members | W | R | R | R | R | R | |||||||
| Project (create) | |||||||||||||
| Public models | R | R | R | R | R | R | R | R | R | R | R | R | |
| Service tokens | |||||||||||||
| Webhooks | W | W | W |
Project permissions for project roles
| Project-level permission | Admin | Analyst | Database admin | Developer | Git Admin | Job admin | Job runner | Job viewer | Metadata (Discovery API only) | Semantic Layer | Stakeholder | Team admin | Webhook |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Data platform connections | W | R | W | R | R | R | R | R | |||||
| Environment credentials (deployment) | W | W | W | W | R | W | R | R | |||||
| Custom env. variables | W | W | W | W | W | W | R | R | W | ||||
| Data platform configurations | W | W | W | W | R | W | R | R | |||||
| Develop (IDE or dbt Cloud CLI) | W | W | W | ||||||||||
| Environments | W | R | R | R | R | W | R | R | R | ||||
| Jobs | W | R | R | W | R | W | R | R | R | R | |||
| Metadata GraphQL API access | R | R | R | R | R | R | R | R | R | R | |||
| Permissions (Groups & Licenses) | W | R | R | R | R | ||||||||
| Profile (Credentials) | W | R | R | R | R | R | |||||||
| Projects | W | W | W | W | W | R | R | R | W | ||||
| Repositories | W | R | R | W | R | R | |||||||
| Runs | W | R | R | W | R | W | W | R | R | R | |||
| Semantic Layer config | W | R | W | R | R | R | W | R | R |
How to set up RBAC Groups in dbt Cloud
Role-Based Access Control (RBAC) is helpful for automatically assigning permissions to dbt admins based on their SSO provider group associations. RBAC does not apply to model groups.
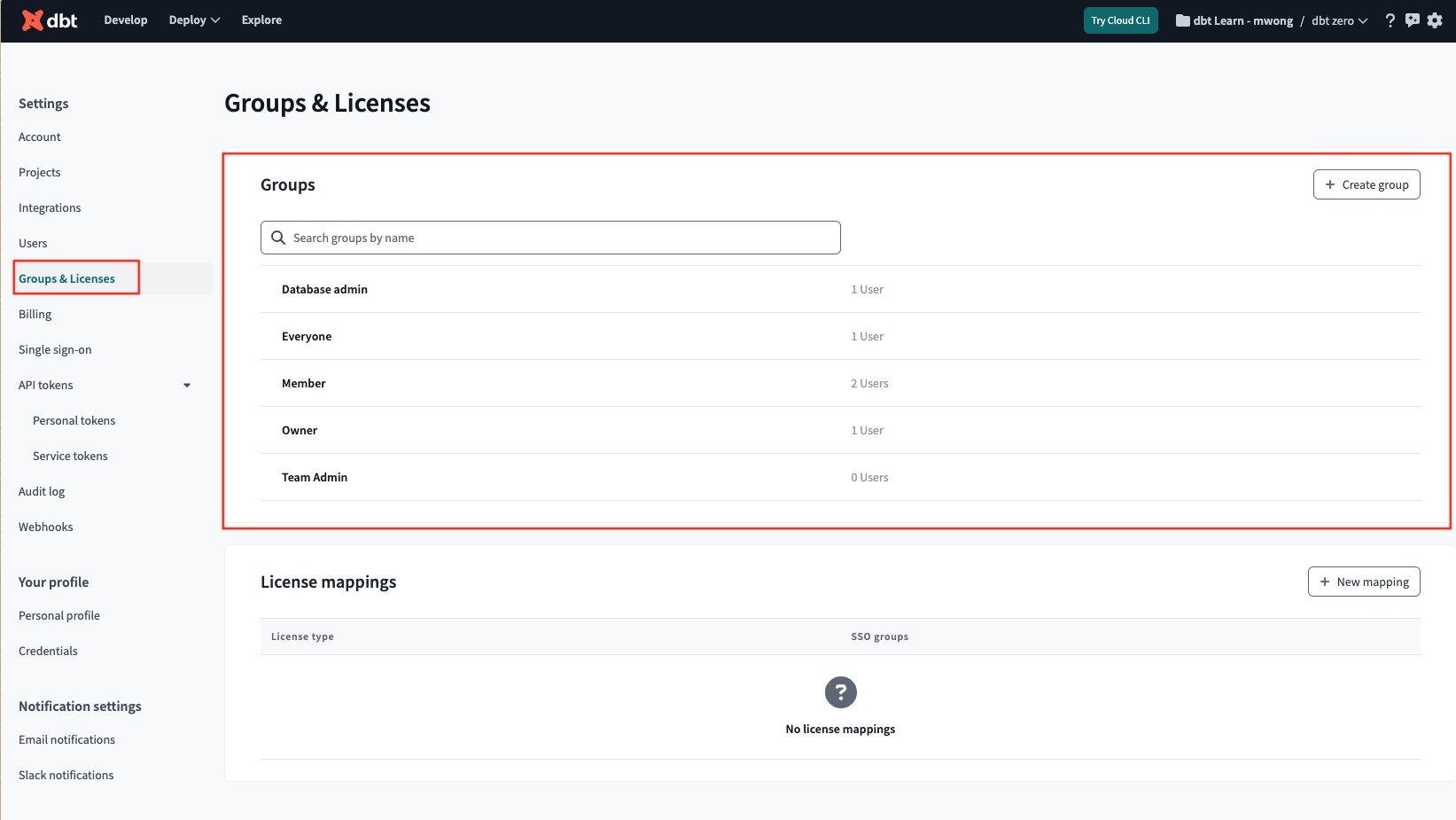
- Click the gear icon to the top right and select Account Settings. Click Groups & Licenses
- Select an existing group or create a new group to add RBAC. Name the group (this can be any name you like, but it's recommended to keep it consistent with the SSO groups). If you have configured SSO with SAML 2.0, you may have to use the GroupID instead of the name of the group.
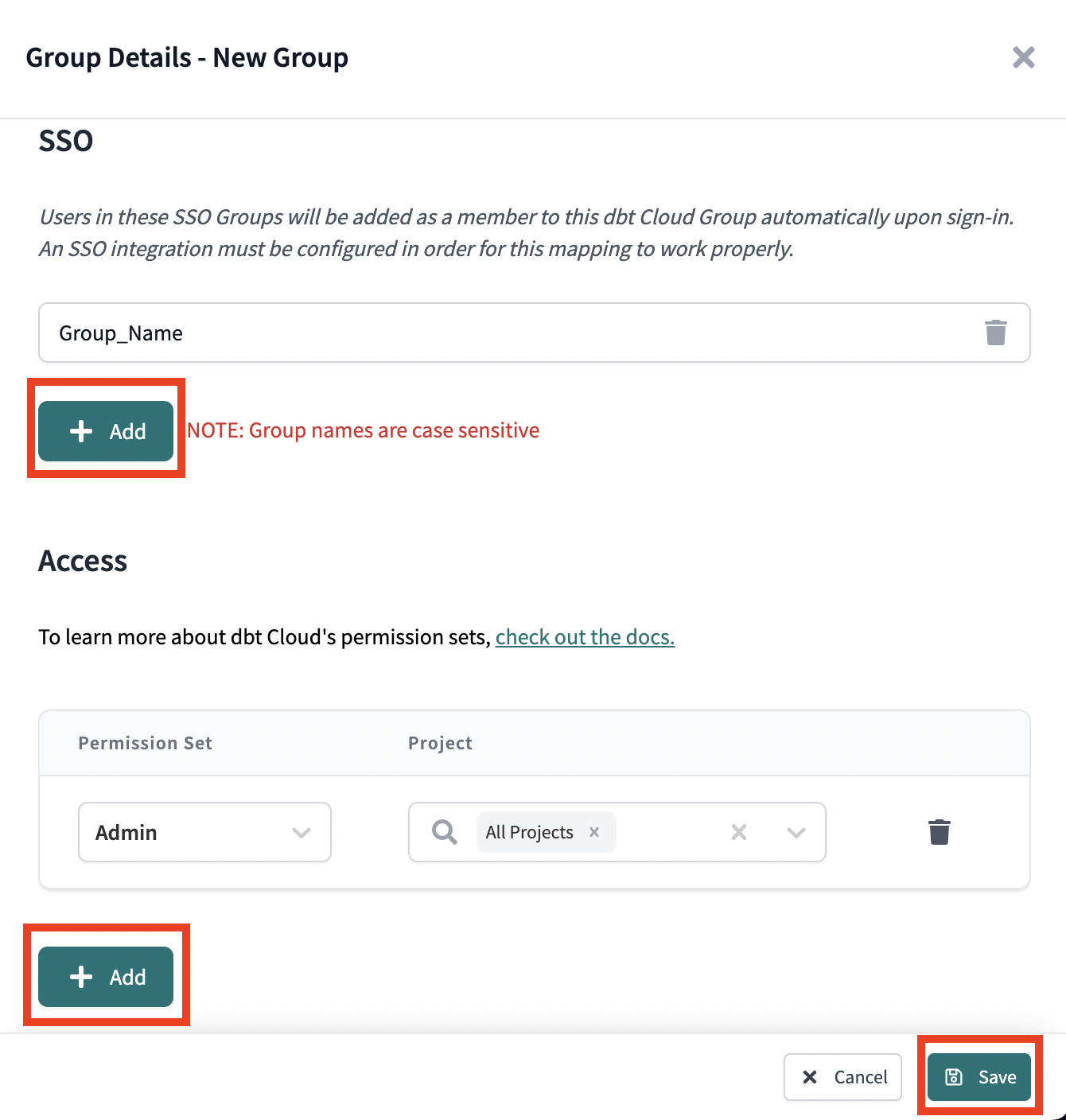
- Configure the SSO provider groups you want to add RBAC by clicking Add in the SSO section. These fields are case-sensitive and must match the source group formatting.
- Configure the permissions for users within those groups by clicking Add in the Access section of the window.
- When you've completed your configurations, click Save. Users will begin to populate the group automatically once they have signed in to dbt Cloud with their SSO credentials.