About user access in dbt Cloud
User groups and access and model groups and access mean two different things. "Model groups and access" is a specific term used in the language of dbt-core. Refer to Model access for more info on what it means in dbt-core.
dbt Cloud administrators can use dbt Cloud's permissioning model to control user-level access in a dbt Cloud account. This access control comes in two flavors: License-based and Role-based.
- License-based Access Controls: User are configured with account-wide license types. These licenses control the specific parts of the dbt Cloud application that a given user can access.
- Role-based Access Control (RBAC): Users are assigned to groups that have specific permissions on specific projects or the entire account. A user may be a member of multiple groups, and those groups may have permissions on multiple projects.
License-based access control
Each user on an account is assigned a license type when the user is first invited to a given account. This license type may change over time, but a user can only have one type of license at any given time.
A user's license type controls the features in dbt Cloud that the user is able to access. dbt Cloud's three license types are:
- Developer — User may be granted any permissions.
- Read-Only — User has read-only permissions applied to all dbt Cloud resources regardless of the role-based permissions that the user is assigned.
- IT — User has Security Admin and Billing Admin permissions applied regardless of the role-based permissions that the user is assigned.
For more information on these license types, see Seats & Users.
Role-based access control
Role-based access control is a feature of the dbt Cloud Enterprise plan
Role-based access control allows for fine-grained permissioning in the dbt Cloud application. With role-based access control, users can be assigned varying permissions to different projects within a dbt Cloud account. For teams on the Enterprise tier, role-based permissions can be generated dynamically from configurations in an Identity Provider.
Role-based permissions are applied to groups and pertain to projects. The assignable permissions themselves are granted via permission sets.
Groups
A group is a collection of users. Users may belong to multiple groups. Members of a group inherit any permissions applied to the group itself.
Users can be added to a dbt Cloud group based on their group memberships in the configured Identity Provider for the account. In this way, dbt Cloud administrators can manage access to dbt Cloud resources via identity management software like Microsoft Entra ID (formerly Azure AD), Okta, or GSuite. See SSO Mappings below for more information.
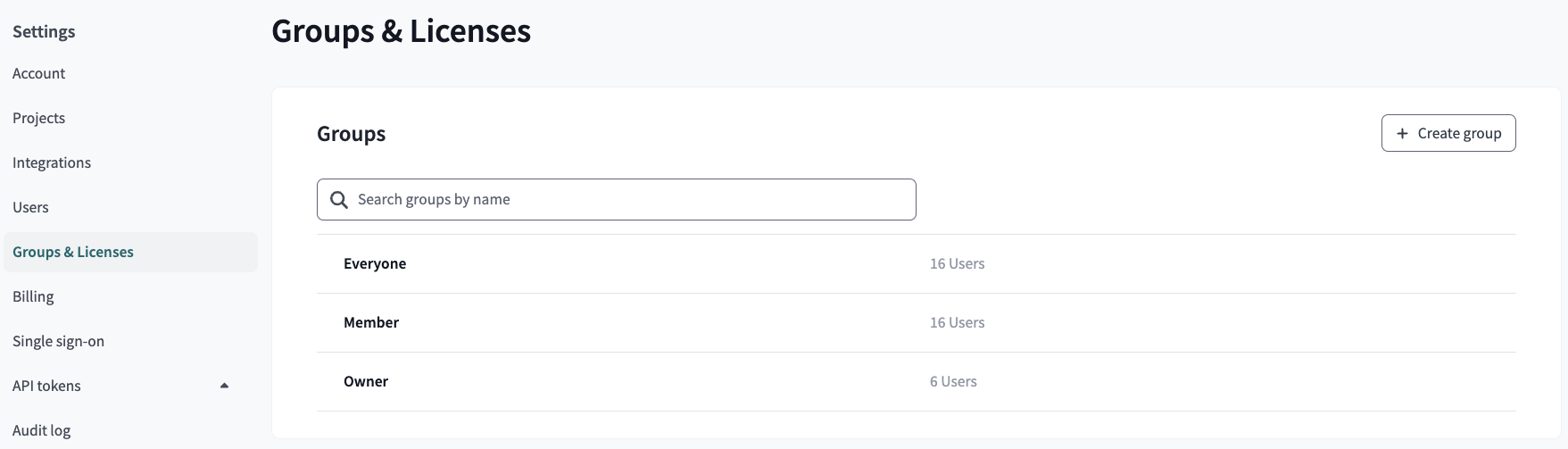
You can view the groups in your account or create new groups from the Groups & Licenses
page in your Account Settings.
SSO mappings
SSO Mappings connect Identity Provider (IdP) group membership to dbt Cloud group membership. When a user logs into dbt Cloud via a supported identity provider, their IdP group memberships are synced with dbt Cloud. Upon logging in successfully, the user's group memberships (and therefore, permissions) are adjusted accordingly within dbt Cloud automatically.
While dbt Cloud supports mapping multiple IdP groups to a single dbt Cloud group, we recommend using a 1:1 mapping to make administration as simple as possible. Consider using the same name for your dbt Cloud groups and your IdP groups.
Permission sets
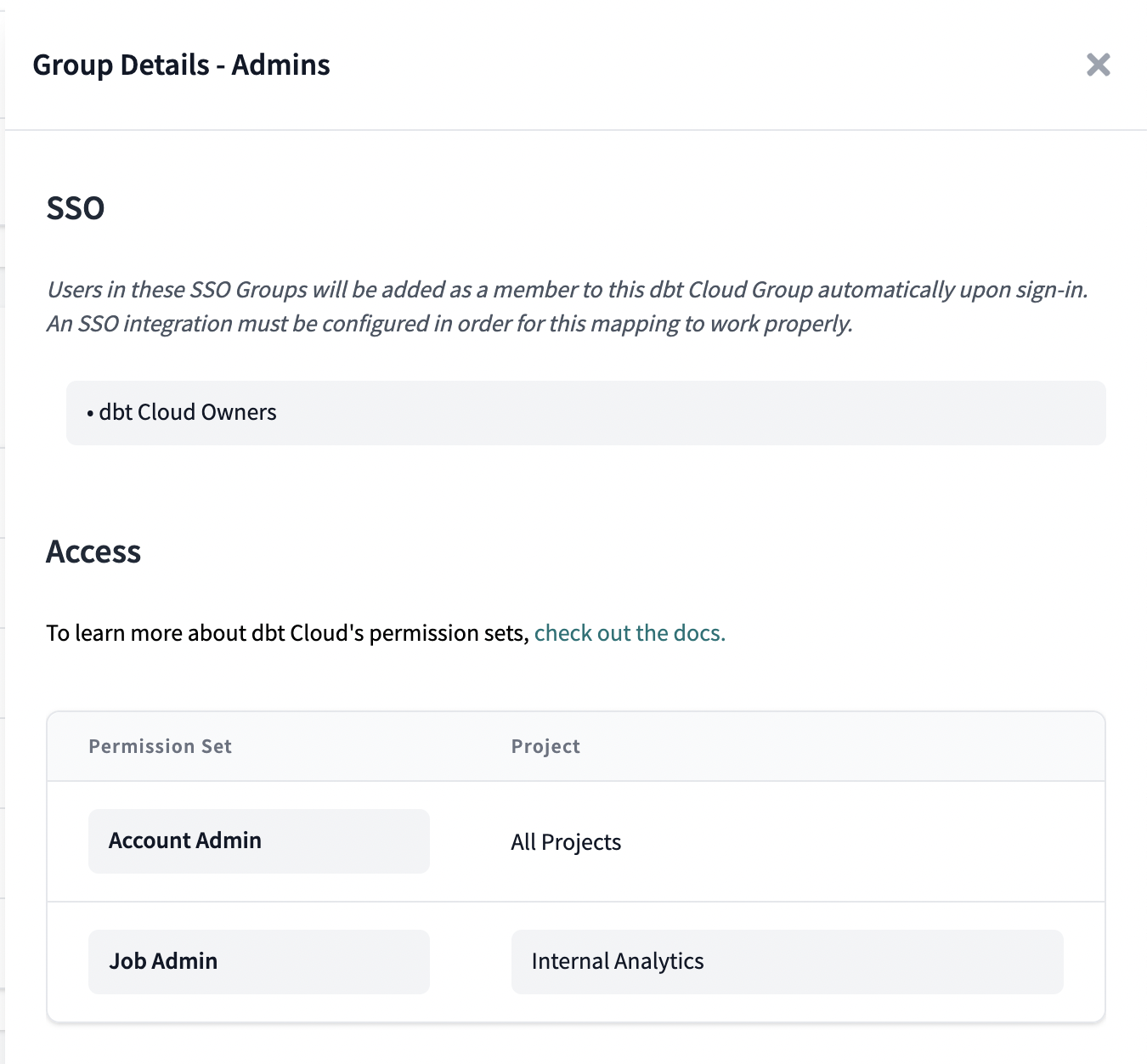
Permission sets are predefined collections of granular permissions. Permission sets combine low-level permission grants into high-level roles that can be assigned to groups. Some examples of existing permission sets are:
- Account Admin
- Git Admin
- Job Admin
- Job Viewer
- ...and more
For a full list of enterprise permission sets, see Enterprise Permissions. These permission sets are available for assignment to groups and control the ability for users in these groups to take specific actions in the dbt Cloud application.
In the following example, the dbt Cloud Owners group is configured with the Account Admin permission set on All Projects and the Job Admin permission set on the Internal Analytics project.
Manual assignment
dbt Cloud administrators can manually assign users to groups independently of IdP attributes. If a dbt Cloud group is configured without any SSO Mappings, then the group will be unmanaged and dbt Cloud will not adjust group membership automatically when users log into dbt Cloud via an identity provider. This behavior may be desirable for teams that have connected an identity provider, but have not yet configured SSO Mappings between dbt Cloud and the IdP.
If an SSO Mapping is added to an unmanaged group, then it will become managed, and dbt Cloud may add or remove users to the group automatically at sign-in time based on the user's IdP-provided group membership information.
FAQs
When are IdP group memberships updated for SSO Mapped groups?
Group memberships are updated whenever a user logs into dbt Cloud via a supported SSO provider. If you've changed group memberships in your identity provider or dbt Cloud, ask your users to log back into dbt Cloud to synchronize these group memberships.Can I set up SSO without RBAC?
Yes, see the documentation on Manual Assignment above for more information on using SSO without RBAC.Can I configure a user's License Type based on IdP Attributes?
Yes, see the docs on managing license types for more information.Why can't I edit a user's group membership?
Make sure you're not trying to edit your own user as this isn't allowed for security reasons. To edit the group membership of your own user, you'll need a different user to make those changes.How do I add or remove users?
Each dbt Cloud plan comes with a base number of Developer and Read-Only licenses. You can add or remove licenses by modifying the number of users in your account settings.If you're on an Enterprise plans and have the correct permissions, you can add or remove developers by adjusting your developer user seat count in Account settings -> Users.
If you're on a Team plan and have the correct permissions, you can add or remove developers by making two changes: adjust your developer user seat count AND your developer billing seat count in Account settings -> Users and then in Account settings -> Billing.
Refer to Users and licenses for detailed steps.